A decommissioned laptop leaves the building. IT wiped the drive. The device is gone. As far as most organisations are concerned, that’s the end of the story. It isn’t.
The moment that device exits your custody without a verified, documented record of what happened to the data on it, you have created a compliance liability — one that an auditor, a regulator, or a plaintiff’s attorney can exploit. The average cost of a data breach now sits at $4.44 million globally, and $10.22 million in the United States alone. These numbers don’t only come from hackers breaching perimeters. They come from retired hardware that shouldn’t have left the building the way it did.
A Certificate of Data Destruction (CoDD) is the document that closes that gap. This post explains what it is, why it matters, and why generating one automatically — on every wipe, every time — is the only defensible standard in 2026.
What a Certificate of Data Destruction Actually Is
A Certificate of Data Destruction is an auditable record confirming that all data stored on a device or storage medium has been permanently and verifiably erased. It is not a receipt. It is not a checkbox. It is a legally defensible document that proves a specific process was applied to a specific asset at a specific point in time.
To be defensible, a CoDD must contain:
- Device identification — serial number, make, model, asset tag
- The erasure standard applied — NIST 800-88, DoD 5220.22-M, or equivalent
- Verification result — pass/fail with method of confirmation
- Technician identity and credentials
- Timestamp and location of erasure
- Parent-child relationship — the link between the storage device and the machine or user it came from
- Software name and version used to perform the wipe
NIST 800-88 Rev.2, the governing standard for media sanitization in the US — and widely adopted internationally — specifically recommends a certificate of sanitization for every sanitized asset. If your CoDD doesn’t capture all of the above, it will not hold up under scrutiny.
The Regulatory Landscape: What the Law Actually Expects
Data destruction is not a best practice. For most organisations, it is a legal obligation — and the certificate is the proof of compliance.
Here is what the primary frameworks require:
| Framework | CoD Requirement | Max Penalty |
|---|---|---|
| NIST 800-88 | Certificate of sanitization recommended per asset | Basis for federal audit failure |
| HIPAA | Documented destruction of PHI required at end-of-life | Up to $1.5M/year per violation |
| GDPR | Erasure must be verifiable; Art. 5 accountability principle | €20M or 4% global turnover |
| PCI DSS | Cardholder data must be rendered unrecoverable; evidence required | Up to $500K per incident |
| GLBA | Safeguards Rule mandates documented disposal of customer data | FTC enforcement action |
| SOX | Executives personally liable for data management failures | $5M fine / 20yr imprisonment |
| FACTA | Consumer report data must be destroyed; documentation implied | FTC civil penalty |
One point that often surprises organizations: the FTC has pursued enforcement actions for inadequate data destruction practices even in the absence of a specific sector regulation. If your organisation handles consumer data — which covers almost everyone — you are exposed.
Without a certificate, you cannot prove that sensitive data was properly erased — and that gap creates liability in legal proceedings, compliance investigations, and failed audits.
The MSP Problem: Your Liability Doesn't End at the Device
For MSPs, the stakes are compounded. You are not just managing your own compliance — you are operating inside the compliance perimeter of every client you serve. That means healthcare, financial services, legal, education, and government clients all flow their regulatory obligations directly to you.
The GLBA Safeguards Rule is explicit: financial institutions are held accountable for the security practices of their vendors. If an MSP handles device retirement for a financial services client and cannot produce a CoDD for every wiped asset, that client is exposed — and so is the MSP.
This creates two realities that every MSP needs to internalize:
First, inherited liability. If a device you managed surfaces data after decommissioning, the chain of custody question lands on your desk. Without a certificate, there is no chain of custody. Without a chain of custody, you have no defense.
Second, competitive differentiation. MSPs that deliver a signed, audit-ready certificate with every wipe are not just protecting themselves — they are providing a deliverable that their clients need. The CoDD is a service line, not an overhead. Forward-looking MSPs are building this documentation into client-facing reporting and using it to justify premium positioning against competitors who are still treating device retirement as an afterthought.
If you are an MSP and you cannot hand a client a certificate after every endpoint retirement, you are the weakest link in their compliance chain.
The Enterprise Problem: Volume, Sprawl, and Audit Readiness
Large enterprises face a different version of the same problem. It is not that they don’t know certificates matter — it is that generating and managing them at scale is operationally complex when done manually. An enterprise retiring several hundred/thousand endpoints a year across multiple sites, teams, and device types has a documentation challenge that spreadsheets and manual processes cannot solve reliably.
When an auditor asks for proof of destruction on a specific device — one that left the organisation 18 months ago — the ability to surface that certificate quickly and easily is what determines whether that audit passes or fails. The certificate must be searchable by asset, by department, by date, by wipe standard, and by technician. It must be tamper-resistant. And it must be complete — no gaps in the record.
Enterprises operating under SOC 2, ISO 27001, or CMMC requirements will find that auditors are increasingly treating the presence of systematic CoDD generation as an indicator of overall security program maturity. A gap in the record is read as a gap in the program.
Why 'We Already Delete Everything' Is Not a Defense
This is the objection we hear most often, and it is worth being direct about why it fails.
A factory reset does not wipe a drive. It removes the file table. The data remains physically present on the storage medium and is recoverable with freely available tools. The same is true of a standard format. Even a BitLocker-encrypted drive that has been ‘wiped’ via a Windows reinstall may retain encrypted data that becomes accessible if the key is ever recovered.
True data erasure requires an overwrite process aligned to a recognised standard — one that renders the data physically unrecoverable and can be independently verified. NIST 800-88 defines three levels: Clear, Purge, and Destroy. The method required depends on the sensitivity of the data and the destination of the device. Simply deleting files satisfies none of them.
The legal point is equally important. Even if you did perform a proper wipe, without a certificate, you cannot prove it. In a regulatory investigation or civil litigation, the burden is on you to demonstrate that proper processes were followed. “We wiped it” is not evidence. A signed, timestamped, software-verified certificate is.
The wipe is the process. The certificate is the outcome that matters to auditors, regulators, clients, and insurers — and without it, the wipe might as well not have happened.
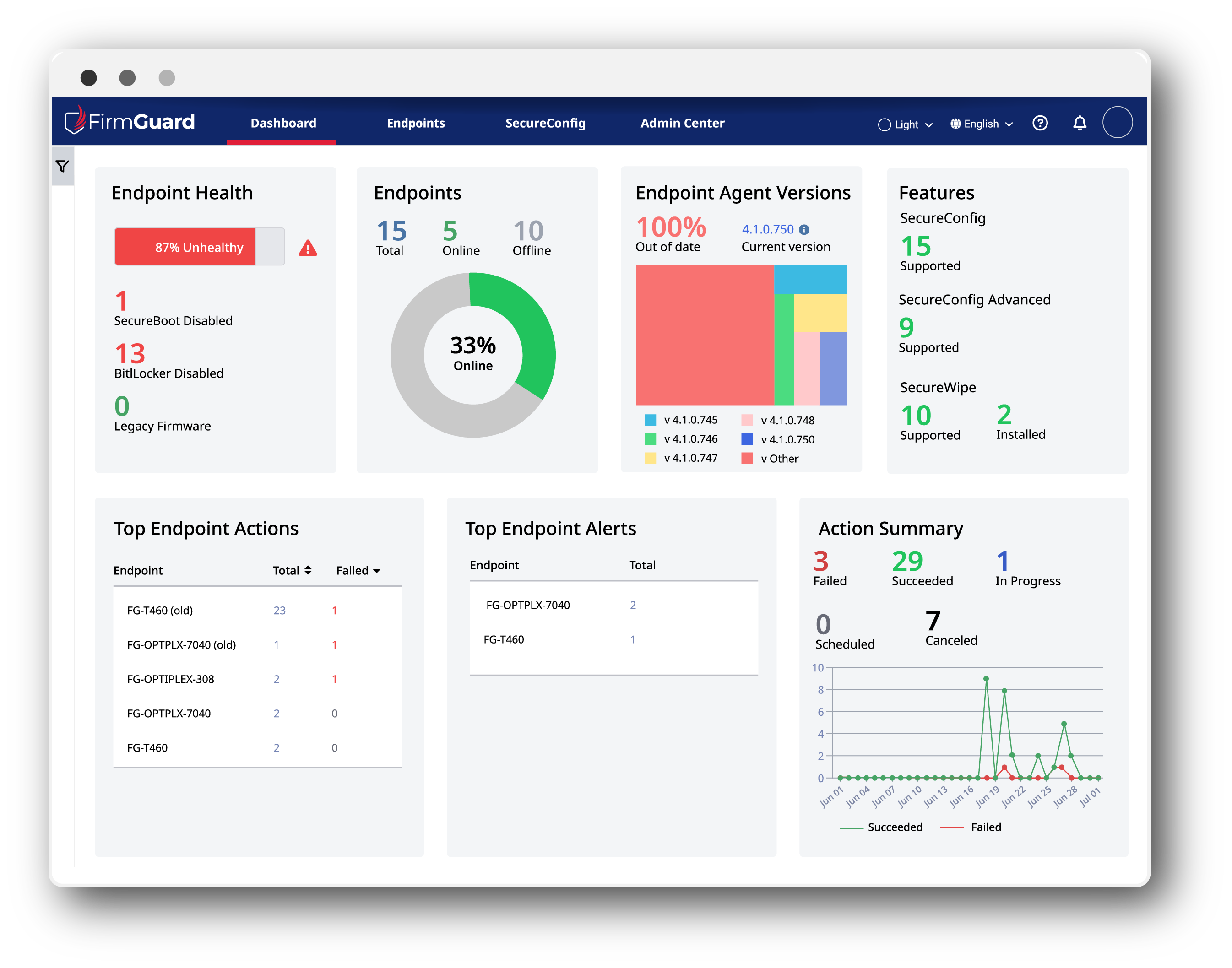
What SecureWipe™ Does Differently
FirmGuard SecureWipe™ is built around the principle that documentation is not a post-process. It is part of the wipe.
The moment a SecureWipe™ erasure completes and passes verification, a tamper-resistant certificate is generated automatically — capturing all seven required fields, signed with the technician’s credentials, and logged to a centralised repository. There is no manual step. There is no delay. There is no risk of a wipe occurring without a record.
For MSPs, this means every device retirement produces a client-ready deliverable that can be included in monthly reporting, attached to service tickets, or surfaced on demand during a client audit. For enterprise IT and compliance teams, it means a searchable, filterable archive of every wipe ever performed — accessible in seconds, not days.
SecureWipe™ supports NIST 800-88 (Clear, Purge), DoD 5220.22-M, and HMG IS5 Baseline and Enhanced — covering the full range of standards your clients and auditors expect to see cited on a certificate.
The Bottom Line
Every endpoint that leaves your custody without a verified certificate of data destruction is an undocumented liability. It doesn’t matter whether the device was wiped correctly if you cannot prove it. And it doesn’t matter how robust the rest of your security program is if device retirement is handled informally.
Regulators, auditors, and clients are not getting less rigorous about this. The frameworks are tightening, the penalties are increasing, and the expectation that organisations can produce complete, verifiable records of data destruction on demand is now baseline.
The certificate is not a formality. It is the proof of work that makes everything else defensible.